-->
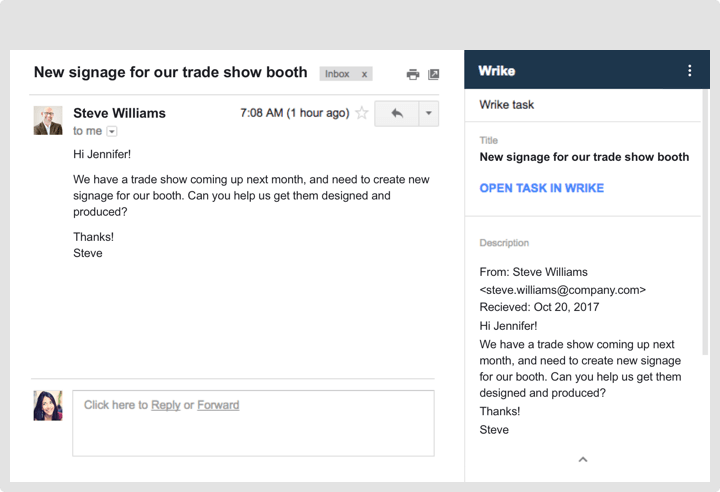
Wrike is an online collaboration tool: easy to plan and to get things done. You are welcome to use it starting now. Invite your peers, clients or subordinaries to use Wrike and work on your. Download Wrike - Project Management apk for PC/Mac/Windows 7,8,10 Choilieng.com helps you to install any apps/games available on Google Play Store. You can download apps/games to PC desktop with Windows 7,8,10 OS, Mac OS, Chrome OS or even Ubuntu OS. Wrike project management free download - Wrike - Project Management, Wrike: Project Management & Collaboration., Project Management Template for Excel, and many more programs.
Top 10 Free macos 10.14 Productivity Apps 1. PDFelement for Mac. PDFelement for Mac is one of the best productivity macOS 10.14 apps for various mac products to view PDF files, edit and manipulate pages, secure and store information, change text and fill out PDF forms. This video demonstrates Office Timeline's integration with Wrike. It will show you how to log-in to Wrike accounts and browse for your project from inside PowerPoint. The tutorial will also show you how to choose which milestones and tasks to import and includes some formatting tips and tricks.
Last updated by the developer on: October 30, 2019
General information
Information provided by Wrike Inc. to Microsoft:
| Information | Response |
|---|---|
| App name | Wrike for Office Documents |
| ID | WA104379841 |
| Office 365 clients supported | Excel 2016 or later on Windows, Word 2013 or later on Windows, PowerPoint 2013 or later on Windows, Excel 2016 or later on Mac, Excel on the web, Word 2016 or later on Mac, Word on the web, PowerPoint 2016 or later on Mac, PowerPoint on the web |
| Partner company name | Wrike Inc. |
| Physical address | 70 N 2nd Street San Jose, CA 95113 |
| URL of partner website | https://wrike.com/ |
| URL of Privacy Policy | https://www.wrike.com/privacy |
| URL of Terms of Use | https://go.microsoft.com/fwlink/?LinkID=521715&omkt=en-US |
| Main telephone number | 1 (877)779-7453 |
| Description of available licensing options, if any | Free, Pro, Business, Enterprise, Wrike for Marketers. Licensing plans described here: https://www.wrike.com/price/ Wrike for Teams does not require a paid plan to be used. |
| Licensing contact | sales@team.wrike.com |
| Licensing telephone number | 1 (877)779-7453 |
Feedback
Questions or updates to any of the information you see here? Contact us!
How the app handles data
Hard disk manager for mac download. Information provided by Wrike Inc. on how this app collects and stores organizational data, and what control an organization has over this data.
Data access using Microsoft Graph
This application does not use Microsoft Graph.
Data access using other Microsoft APIs
Apps and add-ins built on Microsoft 365 may use additional Microsoft APIs other than Microsoft Graph to collect or process organizational information. List any Microsoft APIs other than Microsoft Graph this app uses, and for each, the justification and purpose (what does the app use this information for?), and whether the app stores any of this information in its databases.
| Microsoft API | Justification/Purpose | Is any of this data stored in app database(s)? |
|---|---|---|
| JavaScript API for Office | The add-in uses the Office.js API to integrate with the Office application. | No organizational data is stored in Wrike's databases. |
Non-Microsoft Services Used
If the app transfers or shares organizational data with non-Microsoft service(s), list the non-Microsoft service(s) the app uses, what data is transferred, and include a justification for why the app needs to transfer this information.
Wrike has the integrations with the following vendors which have access to some data:Marketo is email lead capturing services - only names and emails are provided to them.Outreach is Cloud-based sales engagement - only names and emails are provided to them.Salesforce CRM system - has contact information and billing (no sensitive data) information of customers.Zuora - billing and invoicing customers.There is a DPA in place for all the vendors.
Data access via bots
If this app contains a bot or a messaging extension, it can access the roster (first name, last name, display name, email address) of any team member in a team or chat it's added to. Does this app make use of this capability?
Our app creates data only on our side
| Access team/chat roster? | Justification/Purpose | Is any of this data stored in app database(s)? |
|---|---|---|
| No | No | No |
Add-in Data Access
Wrike Free
List the permissions this app requires for accessing your organization's data, the justification and purpose for this permission (what does the app use this information for?), and whether the app stores any of this information in its databases.
| Permission | Description |
|---|---|
| ReadWrite Document | Can read and make changes to your document |
| Send Data | Can send data over the Internet |
Telemetry data
Does any organizational information, including EUII (end-user identifiable information) and OII (organizational identifiable information), appears in this application's telemetry/logs? If yes, describe what data is present and what controls/processes an organization has in place to archive and/or delete it. If no, describe the controls/processes in place to prevent EUII and OII from appearing in telemetry/logs.
No
Storing and securing organizational data
Describe where/how is this application's data is stored and how access to it is controlled. Is it encrypted? Who can access it? How do you ensure that only authorized systems/individuals can access it? Examples: 2FA for all admins, Privileged Access Management (PMA), partitioning service admin accounts from Azure AD/corporate user accounts, protected IP ranges between systems, etc.
Our customers' administrators control all data in their accounts, including deletion/retention/auditing/etc.
Organizational controls for data stored by partner
Describe any capabilities an organization's administrators have to control their information residing in partner systems, e.g. deletion, retention, auditing, archiving, end-user policy, etc.
Call of duty 1 mac download free full version. Experience the classic Call of Duty first-person combat in our new free battle royale game. Download Call of Duty Warzone now.
Wrike has a multi-tenant architecture that logically segregates customers' data through access control based on customer metadata. This metadata is associated with the specific tenant and its access rights according to the role-based access rules within the specific Wrike account. Data is logically isolated and segregated, and access to data is only available through the application to ensure security and privacy. Security at the application level blocks tenants from accessing or modifying application data owned by another tenant. Wrike's application has extensive authentication, role-based access control, authorization, and data sharing and control mechanisms (see https://help.wrike.com/hc/en-us/articles/209603589-Access-Roles and https://help.wrike.com/hc/en-us/articles/209602969) that allow data access for authorized users only. Additionally, encryption at rest is applied for user files uploaded to Wrike servers in file storage via both web application and API; the files are automatically encrypted using AES 256-bit encryption. Furthermore, all servers are encrypted at rest using file system encryption, and moreover Wrike offers Wrike Lock add-in for encryption key managed by a customer, see https://www.wrike.com/add-on-wrike-lock/ and https://help.wrike.com/hc/en-us/articles/360012347934-Wrike-Lock. As additional layer of data security, Wrike offers Audit and Reporting functionality that allows administrators to conduct full security reviews while being able to increase visibility into what is happening in their Wrike account, more details can be found at https://help.wrike.com/hc/en-us/articles/209606309-Audit-Reports. Finally, Wrike provides functionality allowing the granular tracking of access roles to help customers fully audit existing data sharing see details at https://help.wrike.com/hc/en-us/articles/360002004534-Access-Reports.Access to customer data can be considered in two cases:
- Access by Wrike Support team: in case of troubleshooting or verifying the issue requires Support to access to your account; that access can only be granted by you only. This is enabled by a system generated security token that you provide out of band to our Support team, allowing Support to delve deeper into solving your problem for a limited amount of time. This systemic approach ensures additional confidentiality for your data stored in Wrike.
- Access by Wrike Operational team: Wrike Operational team is responsible to maintenance and support production environment including monitoring, patching and updating, delivery the new builds to production, etc. The access in this case is strictly prohibited from both procedural and technical aspects, and strong authorization controls including but not limited VPN, 2FA and personal certificate are in place, moreover it is monitored in details using HIDS (Host-based Intrusion Detection System) and reviewed by Wrike Operational Security team. In case of Amazon KMS (Wrike Lock functionality), the customer data is stored encrypted in Wrike database, so the data is not directly or indirectly available by Wrike Operational team, because the data can be decrypted using access to customer s Amazon KMS, that is managed and controlled by the customer only.
Human review of organizational information
Are humans involved in reviewing or analyzing any organizational data that is collected or stored by this app?
No
Feedback
Questions or updates to any of the information you see here? Contact us!
Information from the Microsoft Cloud App Security catalog appears below.
Note
The information on this page is based on a self-attestation report provided by the app developer on the security, compliance and data handling practices followed by the app. Microsoft makes no guarantees regarding the accuracy of the information. Contact us if you believe information about an app is outdated.
Download Wrike App
Feedback
Questions or updates to any of the information you see here? Contact us!
CSA STAR information
Cloud Security Alliance is a not-for-profit organization dedicated to defining and raising awareness of best practices to help ensure a secure cloud computing environment. The CSA maintains the Security, Trust & Assurance Registry (STAR), a free, publicly-accessible registry where cloud-based providers can publish information on security, privacy, and compliance practices. The STAR registry contains three levels of assurance: self-assessment, 3rd-party audit, and continuous monitoring. More information on assurance levels can be found here.
Note
This information is self-reported by Wrike Inc. and directly submitted to and retrieved from CSA STAR. Microsoft is not responsible for the accuracy of this information.
Cloud Security Alliance information page for Wrike Inc.
Download Cloud Security Alliance documents: Self Assessment (updated February 24, 2020)

Hard disk manager for mac download. Information provided by Wrike Inc. on how this app collects and stores organizational data, and what control an organization has over this data.
Data access using Microsoft Graph
This application does not use Microsoft Graph.
Data access using other Microsoft APIs
Apps and add-ins built on Microsoft 365 may use additional Microsoft APIs other than Microsoft Graph to collect or process organizational information. List any Microsoft APIs other than Microsoft Graph this app uses, and for each, the justification and purpose (what does the app use this information for?), and whether the app stores any of this information in its databases.
| Microsoft API | Justification/Purpose | Is any of this data stored in app database(s)? |
|---|---|---|
| JavaScript API for Office | The add-in uses the Office.js API to integrate with the Office application. | No organizational data is stored in Wrike's databases. |
Non-Microsoft Services Used
If the app transfers or shares organizational data with non-Microsoft service(s), list the non-Microsoft service(s) the app uses, what data is transferred, and include a justification for why the app needs to transfer this information.
Wrike has the integrations with the following vendors which have access to some data:Marketo is email lead capturing services - only names and emails are provided to them.Outreach is Cloud-based sales engagement - only names and emails are provided to them.Salesforce CRM system - has contact information and billing (no sensitive data) information of customers.Zuora - billing and invoicing customers.There is a DPA in place for all the vendors.
Data access via bots
If this app contains a bot or a messaging extension, it can access the roster (first name, last name, display name, email address) of any team member in a team or chat it's added to. Does this app make use of this capability?
Our app creates data only on our side
| Access team/chat roster? | Justification/Purpose | Is any of this data stored in app database(s)? |
|---|---|---|
| No | No | No |
Add-in Data Access
Wrike Free
List the permissions this app requires for accessing your organization's data, the justification and purpose for this permission (what does the app use this information for?), and whether the app stores any of this information in its databases.
| Permission | Description |
|---|---|
| ReadWrite Document | Can read and make changes to your document |
| Send Data | Can send data over the Internet |
Telemetry data
Does any organizational information, including EUII (end-user identifiable information) and OII (organizational identifiable information), appears in this application's telemetry/logs? If yes, describe what data is present and what controls/processes an organization has in place to archive and/or delete it. If no, describe the controls/processes in place to prevent EUII and OII from appearing in telemetry/logs.
No
Storing and securing organizational data
Describe where/how is this application's data is stored and how access to it is controlled. Is it encrypted? Who can access it? How do you ensure that only authorized systems/individuals can access it? Examples: 2FA for all admins, Privileged Access Management (PMA), partitioning service admin accounts from Azure AD/corporate user accounts, protected IP ranges between systems, etc.
Our customers' administrators control all data in their accounts, including deletion/retention/auditing/etc.
Organizational controls for data stored by partner
Describe any capabilities an organization's administrators have to control their information residing in partner systems, e.g. deletion, retention, auditing, archiving, end-user policy, etc.
Call of duty 1 mac download free full version. Experience the classic Call of Duty first-person combat in our new free battle royale game. Download Call of Duty Warzone now.
Wrike has a multi-tenant architecture that logically segregates customers' data through access control based on customer metadata. This metadata is associated with the specific tenant and its access rights according to the role-based access rules within the specific Wrike account. Data is logically isolated and segregated, and access to data is only available through the application to ensure security and privacy. Security at the application level blocks tenants from accessing or modifying application data owned by another tenant. Wrike's application has extensive authentication, role-based access control, authorization, and data sharing and control mechanisms (see https://help.wrike.com/hc/en-us/articles/209603589-Access-Roles and https://help.wrike.com/hc/en-us/articles/209602969) that allow data access for authorized users only. Additionally, encryption at rest is applied for user files uploaded to Wrike servers in file storage via both web application and API; the files are automatically encrypted using AES 256-bit encryption. Furthermore, all servers are encrypted at rest using file system encryption, and moreover Wrike offers Wrike Lock add-in for encryption key managed by a customer, see https://www.wrike.com/add-on-wrike-lock/ and https://help.wrike.com/hc/en-us/articles/360012347934-Wrike-Lock. As additional layer of data security, Wrike offers Audit and Reporting functionality that allows administrators to conduct full security reviews while being able to increase visibility into what is happening in their Wrike account, more details can be found at https://help.wrike.com/hc/en-us/articles/209606309-Audit-Reports. Finally, Wrike provides functionality allowing the granular tracking of access roles to help customers fully audit existing data sharing see details at https://help.wrike.com/hc/en-us/articles/360002004534-Access-Reports.Access to customer data can be considered in two cases:
- Access by Wrike Support team: in case of troubleshooting or verifying the issue requires Support to access to your account; that access can only be granted by you only. This is enabled by a system generated security token that you provide out of band to our Support team, allowing Support to delve deeper into solving your problem for a limited amount of time. This systemic approach ensures additional confidentiality for your data stored in Wrike.
- Access by Wrike Operational team: Wrike Operational team is responsible to maintenance and support production environment including monitoring, patching and updating, delivery the new builds to production, etc. The access in this case is strictly prohibited from both procedural and technical aspects, and strong authorization controls including but not limited VPN, 2FA and personal certificate are in place, moreover it is monitored in details using HIDS (Host-based Intrusion Detection System) and reviewed by Wrike Operational Security team. In case of Amazon KMS (Wrike Lock functionality), the customer data is stored encrypted in Wrike database, so the data is not directly or indirectly available by Wrike Operational team, because the data can be decrypted using access to customer s Amazon KMS, that is managed and controlled by the customer only.
Human review of organizational information
Are humans involved in reviewing or analyzing any organizational data that is collected or stored by this app?
No
Feedback
Questions or updates to any of the information you see here? Contact us!
Information from the Microsoft Cloud App Security catalog appears below.
Note
The information on this page is based on a self-attestation report provided by the app developer on the security, compliance and data handling practices followed by the app. Microsoft makes no guarantees regarding the accuracy of the information. Contact us if you believe information about an app is outdated.
Download Wrike App
Feedback
Questions or updates to any of the information you see here? Contact us!
CSA STAR information
Cloud Security Alliance is a not-for-profit organization dedicated to defining and raising awareness of best practices to help ensure a secure cloud computing environment. The CSA maintains the Security, Trust & Assurance Registry (STAR), a free, publicly-accessible registry where cloud-based providers can publish information on security, privacy, and compliance practices. The STAR registry contains three levels of assurance: self-assessment, 3rd-party audit, and continuous monitoring. More information on assurance levels can be found here.
Note
This information is self-reported by Wrike Inc. and directly submitted to and retrieved from CSA STAR. Microsoft is not responsible for the accuracy of this information.
Cloud Security Alliance information page for Wrike Inc.
Download Cloud Security Alliance documents: Self Assessment (updated February 24, 2020)
Feedback
Questions or updates to any of the information you see here? Contact us!
